
Multi-factor authentication (MFA) is a security staple that adds an extra layer of protection to your online accounts. But what if that very security measure could be turned against you? Enter MFA Fatigue, a cunning social engineering attack that bombards you with login requests, aiming to bypass MFA and compromise your accounts.
In this article, we'll explore what MFA fatigue attacks are, how they can infiltrate MFA defences, and how you can defend yourself against them.
What is MFA Fatigue?
MFA Fatigue is a type of social engineering attack technique that targets accounts protected by Multi-Factor Authentication (MFA). Cybercriminals repeatedly send second-factor authentication requests to the victim's devices, email or phone in an attempt to make the user authenticate the criminals' attempt to access their accounts. It is also known as MFA bombing or MFA spamming.
Beyond accessing your accounts or financial information, MFA Fatigue attacks are also used to deposit ransomware software. This means personal information, corporate resources or sensitive data is taken hostage in exchange for large amounts of money.
How does MFA Fatigue work?
The attacker first needs your login credentials to get started. They usually acquire these through other social engineering techniques. Phishing is a cybercrime designed to steal sensitive data such as usernames, passwords, credit card details, and other confidential information that can predate an MFA fatigue attack. In phone attacks, cybercriminals may use "vishing", short for voice phishing, or “smishing” short for SMS phishing, to trick victims into revealing personal information over the phone that is then used to instigate the MFA fatigue attack.
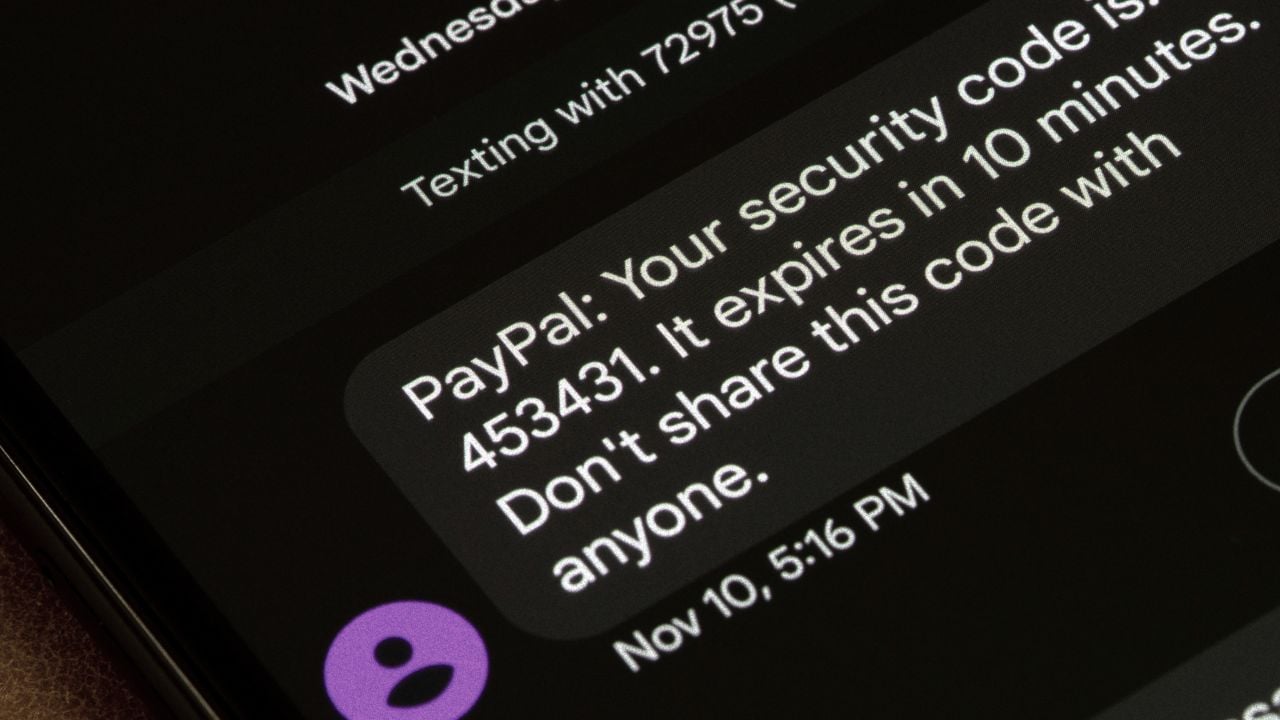
Once the criminal has enough information to access your account they will attempt to log in. While this won't grant them direct access due to MFA, it triggers the system to send approval requests to your phone or email. With each login attempt, even though unsuccessful, the system is programmed to send a notification to your registered device (phone, email) requesting approval. This is exactly what the attacker is trying to trigger.
The aim is to exploit a system designed to enhance security and, by triggering a relentless stream of MFA prompts, wear the victim down. The victim is likely to receive dozens or even hundreds of notifications in a short time, potentially even rendering a device unusable due to the barrage of pop-up notifications.
The attacker doesn't need to MFA codes or even guess at authentication information like a first pet or mother's maiden name. Their goal is to get the victim to approve a fraudulent login attempt out of frustration or simply to make the notifications stop. This brute force style attack is the most aggressive MFA fatigue tactic, the attacker might unleash this rapid sequence of login attempts in a very short timeframe. This aims to overwhelm the system and potentially bypass security measures in place to limit excessive attempts.
However, the attacker might pace the login attempts, sending them at regular intervals over a longer period. This strategy aims to make it seem like legitimate login attempts from different locations, potentially due to travel or using a new device.
How to Defend Against MFA Fatigue Attacks
MFA fatigue attacks bombard you with login requests to bypass the authentication. While they sound sophisticated, defence is possible and relatively simple. By staying alert, using strong verification methods, and recognizing suspicious activity, you can keep these attacks at bay and ensure your accounts remain secure.
1. Be Wary with Any Notifications
You are your own first line of defence. Do not approve any MFA prompts you are not 100% certain of. Always be suspicious and double-check the details before granting access to any of your accounts. Be on the lookout for unrecognized locations or unusual login times. If you do see a notification you weren't expecting, it's best to deny it and report the suspicious activity to the relevant service provider immediately.
2. Limit Login Attempts
Limiting login attempts is a fundamental security measure that significantly hinders MFA fatigue attacks. This means attackers can't trigger a relentless stream of MFA prompts and their strategy to overwhelm you with notification is disrupted. The temporary account lockout after exceeding attempts also forces attackers to wait before trying again. This buys you time to identify suspicious activity and take action. Many platforms can trigger security alerts when login attempts surpass the limit which will notify security teams of potential attacks and allow them to investigate further.
3. Use Strong Second Factors
When it comes to MFA, the type of second factor plays a crucial role in securing your accounts. While SMS notifications are a common choice, attackers can exploit vulnerabilities in mobile networks to redirect your phone number to a SIM card they control. This allows them to intercept the MFA codes sent to your phone, bypassing the security measure altogether.
Security keys are physical devices that require physical possession for login approval. When prompted for MFA, you insert the key into your device, and it transmits a secure confirmation signal. This significantly reduces the risk of unauthorized access, even if your credentials are compromised.
Biometric authentication such as fingerprint scanners, facial recognition, or iris scanners built into your phone or computer can provide a secure and convenient way to verify your identity. Since these features are unique to you, they offer a strong layer of security against unauthorized access.
MFA Fatigue might seem like a sophisticated attack, but with the right knowledge and awareness, you can effectively defend yourself. By staying vigilant about suspicious activity, employing strong second-factor authentication methods, and limiting login attempts, you can significantly reduce the risk of falling victim. MFA remains a valuable security tool. By using it wisely and following the steps outlined above, you can ensure your accounts remain secure and keep cybercriminals at bay.











