AWS vs Azure: What’s the Difference in 2024?
Accedian: Next-gen intrusion detection

The average time to identify a breach in 2019 was 206 days, according to IBM. Do you know if your network has been breached? And what they did afterwards?
Network perimeter protection has certainly increased in sophistication, making it more difficult to breach the perimeter, but cyber criminals have also become more sophisticated in the methods they use to break into networks and then cover their tracks to mask their activities. Once they manage to get past the perimeter, do you have the visibility to detect them and see what the bad actors are doing?
In this guide, find out how next-gen Intrusion Detection Systems (IDS) will help protect you against threats and behaviours that occur once a cyber criminal is able to breach the perimeter.
Recommended Content
Trending Content
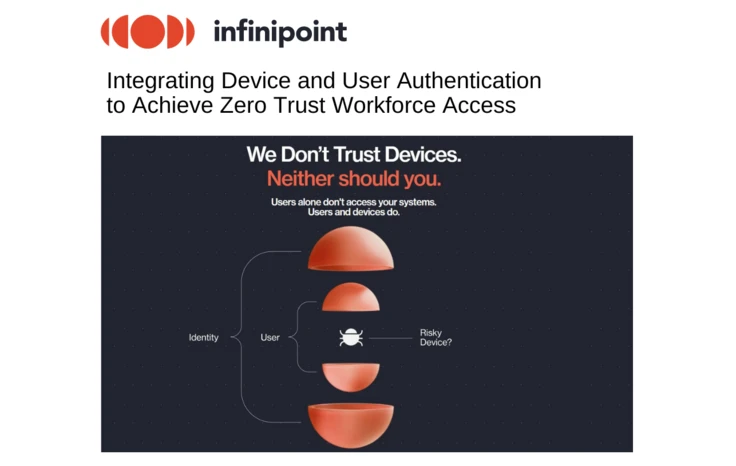
Infinipoint: Integrating Device and User Authentication to Achieve Zero Trust Workforce Access

What is Multi-Cloud Architecture? Definition & Use Cases

Infinipoint - Rethinking Workforce Access: Augmenting Authentication with Zero Device Trust

Meet MAI-1: The New AI Model by Microsoft that Rivals GPT-4

Ministry of Defence Data Exposed in China-Linked Cyber Attack